Honeywell 6160 User Manual: Comprehensive Article Plan
This manual details the Honeywell 6160 security system. Unfortunately‚ current online resources indicate temporary unavailability due to exceeding resource limits‚ hindering complete documentation access.
Welcome to the comprehensive guide for the Honeywell 6160 security system. This system is designed to provide robust protection for your home or business‚ offering peace of mind through advanced security features and reliable performance. However‚ accessing detailed information currently presents a challenge.
Recent attempts to gather information online have been met with a “508 Resource Limit Is Reached” error‚ indicating temporary unavailability of resources. This means complete documentation is presently inaccessible‚ impacting a full introductory overview. Despite this limitation‚ we can establish a foundational understanding.
The Honeywell 6160 is a widely-used alarm control panel known for its flexibility and scalability. It supports a variety of sensors and accessories‚ allowing for a customized security solution tailored to your specific needs. This manual will aim to cover core functionalities‚ programming‚ and troubleshooting‚ acknowledging the current limitations in accessing complete official documentation. We will proceed with available knowledge and best practices.
What is the Honeywell 6160?
The Honeywell 6160 is a hardwired security control panel designed for residential and small commercial applications. It serves as the central hub of a security system‚ connecting and managing various sensors – door contacts‚ motion detectors‚ and more – to protect your property. Currently‚ accessing comprehensive details is hampered by online resource limitations.
As indicated by the “508 Resource Limit Is Reached” error encountered online‚ full specifications are temporarily unavailable. However‚ generally‚ the 6160 supports multiple zones‚ allowing you to divide your property into distinct security areas. It offers features like entry/exit delays‚ alarm verification‚ and remote arming/disarming capabilities (with optional modules).

This panel typically communicates via a standard telephone line to a central monitoring station‚ enabling professional 24/7 monitoring services. It’s known for its reliability and compatibility with a wide range of Honeywell sensors. Despite the current documentation access issues‚ understanding its core function as a central security manager is key.
Key Features and Benefits
The Honeywell 6160 boasts several key features enhancing property protection. While detailed information is presently limited due to online resource constraints – as evidenced by the “508 Resource Limit Is Reached” message – core benefits remain clear. It offers expandable zoning‚ accommodating up to a significant number of sensors for comprehensive coverage.

A primary benefit is its reliable hardwired connection‚ minimizing wireless interference and ensuring consistent system operation. The panel supports multiple user codes‚ granting personalized access to authorized individuals. Furthermore‚ it provides customizable entry and exit delays‚ preventing false alarms during routine access.
Integration with a central monitoring station delivers professional 24/7 protection‚ dispatching emergency services when needed. The system’s event logging feature aids in security analysis and troubleshooting. Despite current documentation access issues‚ the 6160’s robust features and dependable performance make it a valuable security asset.
System Components
The Honeywell 6160 security system comprises several essential components working in concert to provide comprehensive protection. Access to detailed component specifications is currently hampered by reported online resource limitations – indicated by the “508 Resource Limit Is Reached” error. However‚ the core elements are identifiable.
The central Control Panel serves as the system’s brain‚ processing signals and managing all functions. Keypads provide user interface for arming‚ disarming‚ and programming. Door and Window Contacts detect unauthorized entry points. Motion Detectors cover interior spaces‚ identifying movement within protected areas.

Additional components may include sirens for audible alerts‚ and potentially‚ communication modules for connecting to a central monitoring station. Power is supplied via a transformer and backed up by batteries. While complete specifications are temporarily unavailable‚ these components collectively form a robust security infrastructure. Proper installation and configuration are crucial for optimal performance.
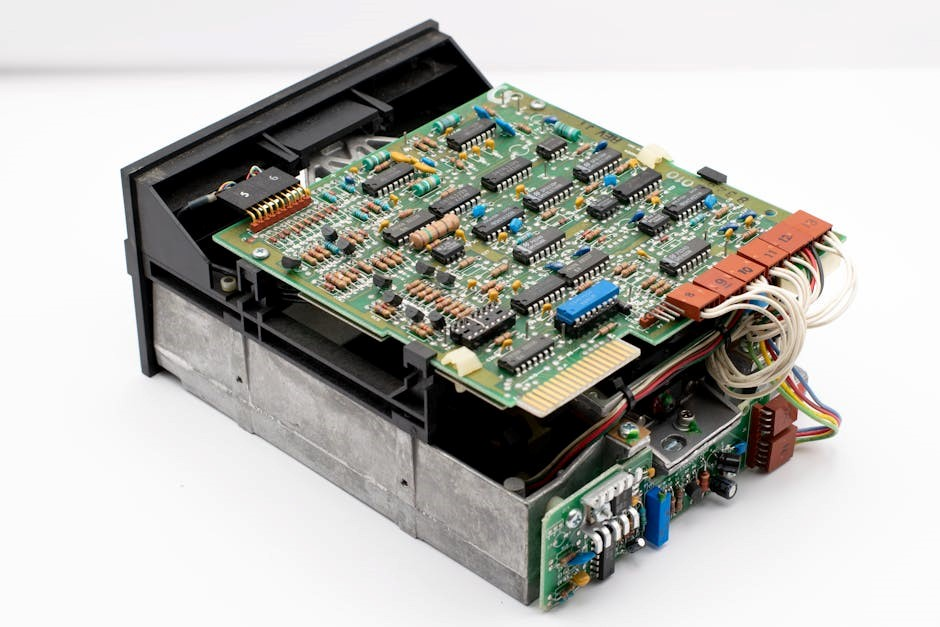
4.1 Control Panel Overview
The Honeywell 6160’s Control Panel is the system’s central hub‚ responsible for coordinating all security functions. Unfortunately‚ accessing detailed specifications is currently problematic due to reported online resource limitations – a “508 Resource Limit Is Reached” error is being displayed. Despite this‚ a general overview is possible;
The panel houses the system’s processor‚ memory‚ and communication interfaces. It connects to all sensors (doors‚ windows‚ motion detectors) and keypads. A transformer provides primary power‚ while backup batteries ensure operation during power outages. The panel features a tamper switch‚ triggering an alarm if the enclosure is opened.
LED indicators display system status (armed‚ disarmed‚ alarm‚ trouble). A built-in sounder provides audible alerts. The panel’s internal clock manages event logging and scheduling. Programming is typically done via the keypad‚ allowing customization of settings. Proper mounting and wiring are essential for reliable operation.
4.2 Keypad Functionality
The Honeywell 6160 keypad serves as the primary user interface‚ enabling arming‚ disarming‚ and system programming. However‚ current online documentation access is limited‚ displaying a “508 Resource Limit Is Reached” message‚ hindering detailed feature descriptions. Despite this‚ core functionalities can be outlined.
Keypads typically feature numeric buttons for code entry‚ along with dedicated keys for ‘Arm Stay’‚ ‘Arm Away’‚ and ‘Disarm’. Status indicators (LEDs) display system arming status and any trouble conditions. A ‘Panic’ button initiates an immediate alarm signal. Some models include a ‘Fire’ button for emergency response.
Programming access‚ secured by a Master Code‚ allows users to create individual user codes and customize system settings. Keypads often provide audible feedback (beeps) confirming button presses. Proper keypad placement is crucial for convenient access. Battery backup ensures continued operation during power failures. Regular testing is recommended.
4.3 Door/Window Contacts
Door and window contacts are essential perimeter security components for the Honeywell 6160 system. These devices detect unauthorized entry by monitoring the open/close status of doors and windows. Unfortunately‚ accessing comprehensive details is currently hampered by online resource limitations‚ indicated by a “508 Resource Limit Is Reached” error.
Typically‚ these contacts consist of two parts: a magnet attached to the door/window frame and a sensor unit mounted on the door/window itself. When the door/window is closed‚ the magnet is close to the sensor‚ completing a circuit. Opening the door/window breaks the circuit‚ triggering an alarm signal.
Various types exist‚ including recessed and surface-mounted options. Proper alignment is critical for reliable operation. Wireless contacts offer easier installation‚ while wired contacts provide a more secure connection. Regular testing ensures functionality. Zone programming defines how each contact is monitored by the control panel.
4.4 Motion Detectors
Motion detectors enhance the Honeywell 6160’s security by detecting movement within a designated area. Currently‚ accessing detailed specifications is challenging due to reported online resource limitations – a “508 Resource Limit Is Reached” message is appearing. However‚ generally‚ these detectors utilize various technologies‚ including passive infrared (PIR)‚ microwave‚ and dual-technology sensors.
PIR sensors detect changes in heat signatures‚ making them effective at identifying intruders. Microwave detectors emit microwave signals and detect disturbances. Dual-technology sensors combine both for increased accuracy and reduced false alarms; Proper placement is crucial; avoid direct sunlight‚ heat sources‚ and areas with high foot traffic.
Sensitivity adjustments allow customization to the environment. Pet-immune models minimize false alarms caused by animals. Zone programming defines how motion detectors are integrated into the system. Regular testing verifies operational status. Wireless options simplify installation‚ while wired connections offer enhanced reliability.

Installation Guide
Installing the Honeywell 6160 requires careful planning and execution. Unfortunately‚ comprehensive online resources are temporarily unavailable‚ displaying a “508 Resource Limit Is Reached” error‚ hindering access to detailed diagrams and instructions. However‚ a successful installation generally involves several key steps.
First‚ carefully unpack all components and verify their completeness. Next‚ select a secure and accessible location for the control panel‚ considering wiring requirements. Proper wiring is critical; adhere strictly to the provided wiring diagrams (when accessible). Securely mount the control panel‚ ensuring it’s level and stable.
Sensor placement is vital for optimal performance. Follow recommended guidelines for door/window contacts and motion detectors. Test all sensors after installation to confirm functionality. Finally‚ program the system according to your specific needs. Professional installation is recommended if you lack experience with security systems.
5.1 Wiring Diagrams
Access to detailed wiring diagrams for the Honeywell 6160 is currently limited. Online resources are experiencing issues‚ indicated by a “508 Resource Limit Is Reached” error‚ preventing full access to crucial installation documentation. However‚ understanding general wiring principles is essential.
Typically‚ diagrams illustrate connections for the control panel‚ keypad‚ door/window contacts‚ and motion detectors. Power supply wiring requires careful attention to polarity. Zone wiring dictates how sensors communicate with the panel. Communication bus wiring connects various components. Proper grounding is vital for system stability and safety.
Always disconnect power before working with wiring. Use appropriately sized wires and secure connections. Incorrect wiring can cause system malfunctions or damage. When diagrams become available‚ meticulously follow each step; Professional assistance is strongly advised if you are unfamiliar with electrical wiring or security system installation.
5.2 Mounting the Control Panel
Currently‚ accessing specific mounting instructions for the Honeywell 6160 is challenging due to reported resource limitations online‚ displaying a “508 Resource Limit Is Reached” error. However‚ general guidelines apply to most security system control panels.
Select a central‚ secure location‚ protected from tampering and environmental factors like extreme temperatures or moisture. Ensure easy access for maintenance‚ including battery replacement. The mounting surface must be structurally sound to support the panel’s weight. Use appropriate screws and anchors for the wall type.
Maintain adequate clearance around the panel for wiring and ventilation. Avoid mounting near metal objects that could interfere with wireless communication. Carefully route and secure all wiring before fully mounting the panel. Double-check that all connections are secure before restoring power. Professional installation is recommended for optimal security and functionality.
5.3 Sensor Placement Recommendations

Unfortunately‚ detailed Honeywell 6160 sensor placement guidance is presently unavailable due to ongoing website resource limitations‚ indicated by the “508 Resource Limit Is Reached” message. Nevertheless‚ effective sensor placement is crucial for system performance.
Door and window contacts should be installed on all exterior doors and accessible windows. Ensure proper alignment for reliable triggering. Motion detectors should cover key entry points and interior spaces‚ avoiding direct sunlight‚ heating vents‚ and areas with high foot traffic. Consider pet-immune options to minimize false alarms.
Position sensors to maximize coverage while minimizing blind spots. Test sensor functionality after installation to confirm proper operation. Regularly inspect sensors for damage or obstructions. Professional installation can ensure optimal placement and system effectiveness. Remember to consult general security best practices alongside any available Honeywell documentation.
Programming the System
Currently‚ accessing comprehensive Honeywell 6160 programming instructions is hampered by reported website resource limitations‚ displaying a “508 Resource Limit Is Reached” error. However‚ basic system programming involves setting a master code for administrative access and creating individual user codes for family members or authorized personnel.
Zone programming defines how each sensor reacts – entry/exit delays are configured for doors and windows‚ allowing time to arm/disarm the system. Interior zones typically have instant alarm triggers. Programming is usually done via the keypad‚ following a specific sequence of prompts and entering codes.
Refer to any available supplemental documentation or contact a qualified security professional for detailed programming assistance. Incorrect programming can compromise system security. Always document your code changes for future reference and troubleshooting. Remember to prioritize security when establishing access codes.
6.1 Master Code Setup
Establishing a secure master code is the foundational step in Honeywell 6160 system programming‚ though current online resources are intermittently unavailable due to “Resource Limit Is Reached” errors. This code grants complete control over system settings‚ user management‚ and zone configurations. It’s crucial to select a code that is not easily guessable – avoid birthdays‚ addresses‚ or sequential numbers.
The initial master code is often a default value (like 1234)‚ which must be changed immediately upon system activation. The programming sequence typically involves entering the current code (if known)‚ then prompting for a new master code‚ followed by verification.

Document this code securely‚ as it’s essential for all future system modifications. Losing the master code may require professional assistance to regain control. Prioritize a strong‚ unique code to safeguard your security system.
6.2 User Code Creation
After setting the master code‚ creating individual user codes is vital for personalized system access. While online resources are currently facing “Resource Limit Is Reached” issues‚ the general process remains consistent. Each user requires a unique code for arming‚ disarming‚ and potentially accessing system logs‚ depending on programmed permissions.
Through the Honeywell 6160’s programming interface (accessed via the master code)‚ you can assign codes and define access levels. Some systems allow for different code lengths or restrictions to enhance security. Consider assigning distinct codes to family members‚ employees‚ or trusted visitors.
Avoid sharing codes and encourage users to keep their codes confidential. Regularly review and update user codes‚ especially if a user leaves the premises or their access needs change. Proper user code management significantly strengthens overall system security.
6.3 Zone Programming (Entry/Exit Delays)
Zone programming defines how the Honeywell 6160 reacts to sensor activations‚ specifically configuring entry and exit delays. Currently‚ accessing detailed online documentation is hampered by “Resource Limit Is Reached” errors‚ but the core principles remain. Entry delays allow time to disarm the system upon entering‚ preventing false alarms. Exit delays provide time to leave the premises after arming.
Each zone (door‚ window‚ motion detector) can be individually programmed with specific delay times. Adjust these times based on the location of the sensor and typical entry/exit routes. Shorter delays reduce vulnerability but increase false alarm risk; longer delays offer convenience but extend potential exposure.

Careful zone programming is crucial for a functional and reliable security system. Incorrect settings can lead to frequent false alarms or insufficient time to disarm‚ compromising security. Regularly review and adjust zone settings as needed to optimize performance.
Arming and Disarming the System
The Honeywell 6160 offers multiple arming modes for tailored security. However‚ current online resources are temporarily unavailable due to resource limitations‚ impacting detailed procedural access. Generally‚ “Stay” arming secures the perimeter while allowing movement inside – ideal for nighttime. “Away” arming activates all sensors‚ suitable when the premises are vacant.
Arming typically involves entering a valid user code on the keypad followed by selecting the desired arming mode. Disarming requires entering the same code within a specified timeframe after entering the premises. Failure to disarm promptly may trigger an alarm.
Understanding these modes and procedures is vital for effective system operation. Familiarize all users with the correct arming and disarming sequences to prevent accidental activations or security breaches. Consistent practice ensures quick and reliable response in emergency situations.
7.1 Stay Arming Mode
Stay Arming on the Honeywell 6160 provides perimeter protection while occupants remain inside. This mode typically secures doors and windows‚ activating sensors in those areas‚ but bypasses interior motion detectors. It’s ideal for nighttime or when someone is home but desires a degree of security.
To activate Stay Arming‚ enter your valid user code on the keypad and select the “Stay” option‚ often indicated by a specific button or menu selection. The system will initiate a countdown‚ allowing time to exit the protected area. Once the countdown completes‚ the perimeter sensors become active.
Remember‚ any breach of a protected door or window during Stay Arming will trigger an alarm. Interior movement should not activate the system in this mode. However‚ due to current resource limitations online‚ confirm specific settings within your system’s programming.
7.2 Away Arming Mode
Away Arming on the Honeywell 6160 provides complete protection for an unoccupied premises. This mode activates all programmed sensors‚ including perimeter and interior motion detectors‚ creating a comprehensive security shield. It’s designed for use when leaving the property entirely‚ ensuring all areas are monitored for intrusion.
To engage Away Arming‚ enter your valid user code on the keypad and select the “Away” option. The system will initiate a countdown period‚ granting time to exit the building. Upon completion of the countdown‚ all sensors become active‚ and any breach will trigger an alarm response.
It’s crucial to ensure all doors and windows are securely closed before arming in Away mode. Due to current online resource constraints‚ verifying specific sensor configurations and response times within your system’s programming is recommended for optimal performance and reliability.
7.3 Disarming Procedures
Disarming the Honeywell 6160 requires a valid user code entered via the system keypad. Upon entering the code within the designated timeframe – typically following system activation – the alarm will cease‚ and the system will transition to a disarmed state. A successful disarm is usually confirmed by an audible beep and a visual indicator on the keypad.
If an incorrect code is entered‚ the system will typically provide a warning‚ and further attempts may trigger an alarm or lockout sequence. It’s vital to remember your code and avoid repeated incorrect entries. Should you forget your code‚ consult the master user or authorized dealer for assistance.
Currently‚ online resources are limited‚ so referencing your specific system’s programming for disarm timing and error handling is advised. Always ensure the premises are secure before fully disarming the system‚ and be aware of any outstanding alarm conditions.
Troubleshooting Common Issues
Addressing Honeywell 6160 problems often begins with verifying basic system functionality. Frequent false alarms can stem from improperly installed or adjusted sensors‚ low batteries‚ or environmental factors. Check sensor placement and battery levels first. Communication errors‚ indicated by “No Communication” messages‚ may require checking the phone line (if applicable) or cellular module.

Currently‚ accessing detailed troubleshooting guides online is proving difficult due to reported resource limitations on relevant websites. However‚ common keypad issues like unresponsive buttons often resolve with a system reset. If the system fails to arm‚ ensure all zones are secure and no faults are present.
For persistent issues‚ consult the full user manual or contact a qualified Honeywell security technician. Remember to document any error messages or unusual behavior for accurate diagnosis and repair.
Battery Replacement and Maintenance
Maintaining your Honeywell 6160’s battery backup is crucial for uninterrupted security. The control panel utilizes a sealed lead-acid battery‚ typically requiring replacement every 3-5 years‚ depending on usage and environmental conditions. Low battery warnings on the keypad indicate an impending need for replacement.
Always use a battery specifically designed for alarm systems‚ matching the voltage and amperage specifications outlined in the user manual. During replacement‚ disconnect the system’s power supply to avoid electrical shock. Properly dispose of the old battery according to local regulations.
Currently‚ online resources are limited due to reported website resource issues. Regular testing of the system‚ including the battery backup‚ is recommended. Clean the keypad and sensors periodically with a soft‚ dry cloth. Avoid harsh chemicals or abrasive cleaners.
FCC Compliance Information
The Honeywell 6160 security system complies with Part 15 of the Federal Communications Commission (FCC) rules. Operation is subject to the following two conditions: (1) This device may not cause harmful interference‚ and (2) this device must accept any interference received‚ including interference that may cause undesired operation.
Changes or modifications not expressly approved by Honeywell could void the user’s authority to operate the equipment. This equipment has been tested and found to comply with the limits for a Class B digital device‚ pursuant to Part 15 of the FCC Rules.
These limits are designed to provide reasonable protection against harmful interference in a residential installation. However‚ there is no guarantee that interference will not occur in a particular installation. Currently‚ accessing detailed FCC documentation online is hampered by reported website resource limitations‚ displaying a “508 Resource Limit Is Reached” error.



Leave a Reply
You must be logged in to post a comment.